- Email Security Training Goals
-
- Learn phishing awareness - what phishing emails look like and how to stop phishing.
- Treat every email as a phishing email until determined otherwise.
- Dispose of phishing (real or simulated) email. In lieu of organization guidance, AnteSpam recommends deleting or notifying IT security if not sure.
- Provide metrics that show training progress and identify users who could benefit from additional instruction.
- Email Security Training Works
-
This is a real graph of real user % fail performance for a real organization using EST (lower is better).
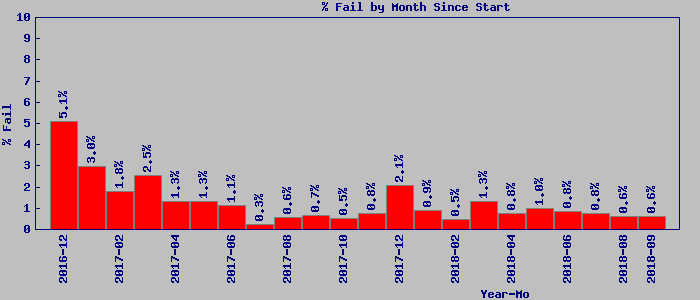
In addition to showing initial improvement, the graph also shows seasonal "danger periods" (holiday and tax season) when additional management emphasis could help staff be more aware. Your organization performance may vary depending on many factors including initial level of expertise and how often and how long EST is enabled for your staff.
EST can also help identify "holes" in security training and procedures. For example, do all your people know how or who to ask to confirm an email really was sent to them from the company President/CEO/COO requesting sensitive data? EST will help show you who doesn't.
- How EST Teaches and Reminds
-
Email Security Training is not a video or seminar training with limited retention. Instead, EST can best be described as a phishing email simulator that provides behavior-based, on-the-job training and reminders in a few seconds, 1 to 4 times a week. Using EST will teach email security best practices to those who need it and remind and update those who don't.
- Why EST Simulator Training Is Better
-
EST training doesn't require time away from work. The simulated phishing emails are sent at random intervals, provide practical experience, and teach email security best practices and habits as the user works. EST also avoids the Ebbinghaus Forgetting Curve through long-term repetition and becoming part of normal routine.
Industry and the military use simulators to teach safe and correct operation of high value equipment in high risk environments and require continued use of simulators for even the most experienced operators. Why? Because simulators are behavior-based learning in a real-world environment with "negative" feedback for the operator's mistakes and "positive" feedback for correct actions. Both industry/military simulators AND EST provide this behavior-based training and their long term use keeps operator skills and knowledge fresh.
Mistakes made in realistic simulations can be embarrassing, but they can also help identify where you need to improve company security training and procedures. An example straight from recent headlines: Do all your people know how or who to ask to confirm an email really was sent to them from the company President/CEO/COO requesting sensitive data? EST will help show you who doesn't.
Sign up for a Free Month! Or Contact an AnteSpam Channel Partner, or get a quote from us for EST Retail Service.
- What the Numbers and Experts Say
-
According to Verizon's Data Breach Investigations Reports, 95% of all espionage attacks and nearly 80% of all malware attacks involve phishing. Another recent report estimates a 22% chance you could have a breach within the next 24 months.
According to different surveys the average cost to a company of a successful spear phishing attack can be $300,000 and higher. A survey published in 2016 by InfoSecurity Magazine puts the average at $1.6 million. In fact, companies may find themselves legally responsible to employees if someone on staff discloses personnel information due to being tricked by a phishing scam.
A quote from a recent news article describes the issue in a nutshell: "To be truly effective in preventing and combating security threats, organizations need to take steps to spread security awareness and knowledge through the entire organization, from the clerk in the mailroom to the CEO in the corner office."
Finally, CSO Online reports that "The average employee wastes 4.16 hours a year on phishing scams."
EST on the other hand requires on average 62.1 minutes per year. For a company with 50 users at an avg of $25/hr, EST will potentially save $3,906.25 in user time over a year while costing $714 or less. And those savings don't include avoiding the impact of a successful phishing attack on your bottom line (ie, cyber ransoms or other malware direct impacts) and your customer's loss of faith in your company and services. For a larger company or organization EST's savings are proportionally greater.
- An Email Security Training overview

AnteSpam is created and operated by Ironic Design, Inc.
Copyright © 2002-2024 Ironic Design, Inc., All Rights Reserved.
Copyright © 2002-2024 Ironic Design, Inc., All Rights Reserved.